當mysql跨越互聯網進行復制時別人可以竊取到mysql的復制信息,這些信息是明文的,因此存在不安全性,這裡通過ssl對復制的信息進行加密。當在客戶沒有固定ip而要訪問服務器時,mysql要允許任意地址的訪問,服務端和客戶端通過證書驗證可以防止暴力破解。
開始之前讓我們先來回顧一下SSL協議客戶端OpenSSL的安裝過程:
安裝openssl
mkdir /test/setup cd /test/setup tar zxvf openssl-0.9.8b.tar.gz cd openssl-0.9.8b ./config make && make install
開啟mysql中ssl功能
登錄Mysql查看
mysql> show variables like '%ssl%';
+---------------+----------+ | Variable_name | Value | +---------------+----------+ | have_openssl | DISABLED | | have_ssl | DISABLED | | ssl_ca | | | ssl_capath | | | ssl_cert | | | ssl_cipher | | | ssl_key | | +---------------+----------+
如果mysql輸出如上所述,那麼繼續操作開啟ssl;如果不是,重新編譯安裝mysql,注意生成makefile時填寫參數正確。
退出mysql,編輯/etc/my.cnf
在[mysqld]和[mysqldump]之間,加入下列配置信息:
ssl
保存後重新啟動mysql,再次登錄mysql
mysql -uroot -p mysql> show variables like '%ssl%';
+---------------+-------+ | Variable_name | Value | +---------------+-------+ | have_openssl | YES | | have_ssl | YES | | ssl_ca | | | ssl_capath | | | ssl_cert | | | ssl_cipher | | | ssl_key | | +---------------+-------+
好了,下面進入正題:
mysql基於ssl復制
1、創建證書中心
在主服務器上創建證書中心
cd /etc/pki/CA
生成私鑰
(umask 077;openssl genrsa -out /etc/pki/CA/private/cakey.pem 2048)
生成自簽證書,由於需要輸入大量用戶信息,因此編輯證書的配置文件,在私有的CA上創建證書要注意所有的用戶信息要和CA中的一致,從國家到部門都要相同,否則會造成證書無法使用
vim /etc/pki/tls/openssh.cnf
[ req_distinguished_name ] countryName = Country Name (2 letter code) countryName_default = CN countryName_min = 2 countryName_max = 2 stateOrProvinceName = State or Province Name (full name) stateOrpovinceName_default = FJ localityName = Locality Name (eg,city) localityName = FZ O.organizationName = Organization Name (eg,company) O.organizationName_default = zdz organizationalUnitName = Organizational Unit Name (eg,section) organizationalUnitName_default = zdz
生成自簽證書
openssl req -new -x509 -key /etc/pki/CA/private/cakey.pem -out /etc/pki/CA/cacert.pem -days 3650
-x509是創建自簽證書是需要的參數,在創建其他證書時不能加該參數
由於是自簽證書因此要修改證書路徑
vim /etc/pki/tls/openssl.cnf
[ CA_defalut ] dir = /etc/pki/CA certs = $dir/certs #存放生成證書的目錄 crl_dir = $dir/crl #存放吊銷證書的目錄 database = $dir/index.txt #證書的索引文件 new_certs_dir = $dir_newcerts #新簽的證書目錄 serial = $dir/serial #序列號 crl = $dir/crl.pem private_key = $dir/private/cakey.pem #證書中心私鑰文件
創建證書編號
mkdir certs crl newcerts touch index.txt echo 00 > serial
2、為主服務器創建證書
服務器的名稱必須固定,在申請證書時要輸入服務器名稱,證書和服務器名稱對應
創建私鑰
mkdir /usr/local/mysql/ssl cd /usr/local/mysql/ssl (umask 077;openssl genrsa -out /usr/local/mysql/ssl/master.key 2048)
生成證書申請
openssl req -new -key master.key -out master.csr
在證書服務器上對master的證書進行簽發
openssl ca -in master.csr -out master.crt -days 365
3、創建從服務器證書
(umask 077;openssl genrsa -out /usr/local/mysql/ssl/slave.key 2048) openssl req -new -key slave.key -out slave.csr
將從服務器的證書申請文件復制到證書服務器上進行簽發
opessl ca -in slave.csr -out slave.crt -days 356
4、修改證書權限和mysql配置文件
將證書的公鑰cacert.pem復制到主從服務器的目錄下
cd /usr/local/mysql/ssl cp /etc/pki/CA/cacert.pem ./ chown -R mysql:mysql master.crt master.key cacert.pem chmod 600 master.crt master.key cacert.pem vim /usr/local/mysql/my.cnf ssl ssl_ca = /usr/local/mysql/ssl/cacrt.pem ssl_cert = /usr/local/mysql/ssl/master.crt ssl_key = /usr/local/mysql/ssl/master.key
修改從服務器配置
cd /usr/local/mysql/ssl cp /etc/pki/CA/cacert.pem ./ chown -R mysql:mysql slave.crt slave.key cacert.pem chmod 600 slave.crt slave.key cacert.pem vim /usr/local/mysql/my.cnf ssl ssl_ca = /usr/local/mysql/ssl/cacrt.pem ssl_cert = /usr/local/mysql/ssl/slave.crt ssl_key = /usr/local/mysql/ssl/slave.key
5、在主服務器上創建復制用戶
grant replication slave on *.* to slave@'192.168.216.133' identified by 'slave' requere ssl; flush privileges;
查看主服務器當前二進制位置
mysql> show master status ;
+-------------------------+------------+---------------------+--------------------------+--------------------------+ | File | Position | Binlog_Do_DB | Binlog_Ignore_DB | Executed_Gtid_Set | +-------------------------+------------+---------------------+--------------------------+--------------------------+ | mysql-bin.000007 | 1015 | | | | +-------------------------+------------+---------------------+--------------------------+---------------------------+ 1 row in set (0.00 sec)
6、在從服務器上開始復制
change master to master_host='192.168.216.132', master_user='slave', master_password='slave', master_log_file='mysql-bin.000007', master_log_pos=1015, master_ssl=1, master_ssl_ca=' /usr/local/mysql/ssl/cacrt.pem', master_ssl_cert='/usr/local/mysql/ssl/slave.crt', master_ssl_key='/usr/local/mysql/ssl/slave.key'; start slave;
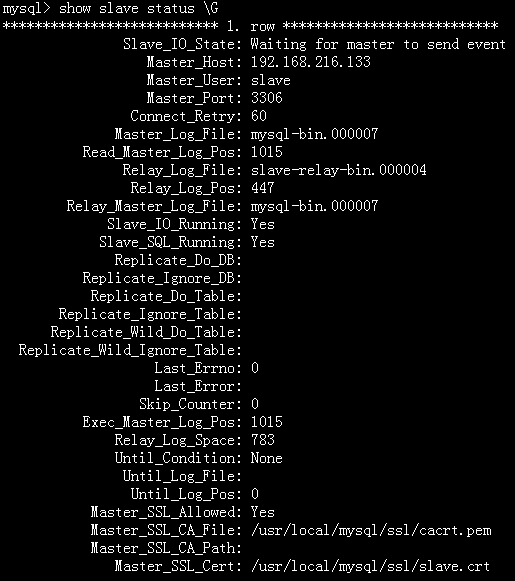
查看狀態
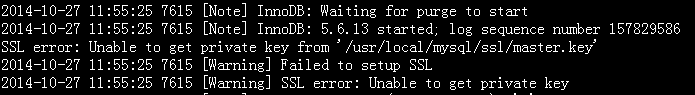
錯誤1:
如果要確保證書沒有問題可以通過建立測試的用戶同ssl進行連接在主服務器上開一個權限很大的用戶,進行ssl的登錄測試
grant all privileges on *.* to root@'192.168.216.133′ identified by ‘root' require ssl; [root@slave ssl]# mysql -uroot -proot -h192.168.216.133 –ssl-ca=cacrt.pem –ssl-cert=slave.crt –ssl-key=slave.key
Warning: Using a password on the command line interface can be insecure. ERROR 2026 (HY000): SSL connection error: ASN: before date in the future
這是由於虛擬的時間不正確導致
如果這時候不使用ssl方式進行連接則會報出錯誤
[root@slave ssl]# mysql -uroot -proot -h192.168.216.133;
Warning: Using a password on the command line interface can be insecure. ERROR 1045 (28000): Access denied for user ‘root'@'192.168.216.132′ (using password: YES)
錯誤2:
在配置文件中添加證書配置後執行 show variables like ‘%ssl%'顯示
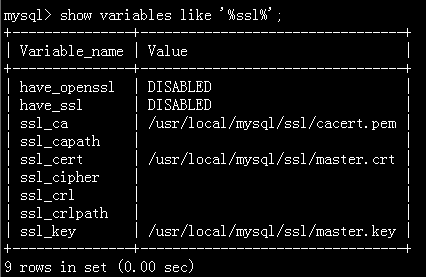
這是由於沒有將證書的屬主改為mysql,可以從日志中得知是無權限獲取私鑰